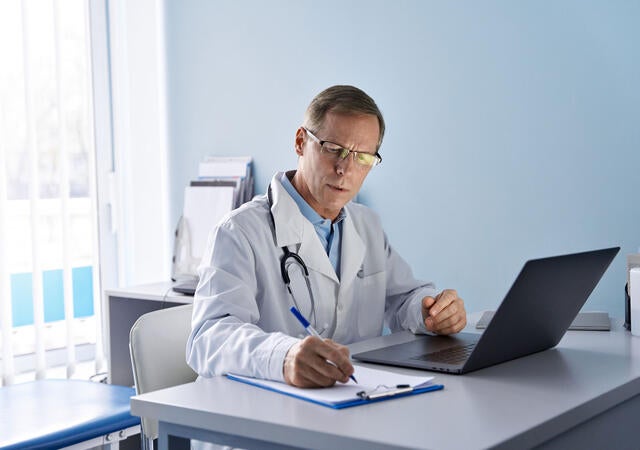
We Specialize in Global Medical Device Compliance and Innovation
Emergo by UL is a leading consulting firm specializing in global regulatory compliance and human factors for products in the medical industry. Our comprehensive services are designed to help you achieve and maintain regulatory and commercial success.
Contact us